Online Privacy
Data Privacy: What Is It and How to Protect Your Data Security?
Data privacy is important for each person. Enterprises and organizations must try their best to protect users' personal information. How to do it? Find it in our blog.
Jul 09, 2024Robin Brown
What Is Data Privacy?
Data privacy (or information privacy) is an area of data protection. It refers to the fact that individuals can decide when, how and to what extent their personal data is shared or exchanged with others.
In other words, data privacy revolves around how a user's personal data is collected, stored, managed, and shared with third parties.
The process of sharing with others may involve how sensitive and other confidential data are handled appropriately to meet regulatory requirements and protect the confidentiality and invariance of the data.
However, Data Privacy Is not Data Security!
Data security and data privacy form the field of data protection:
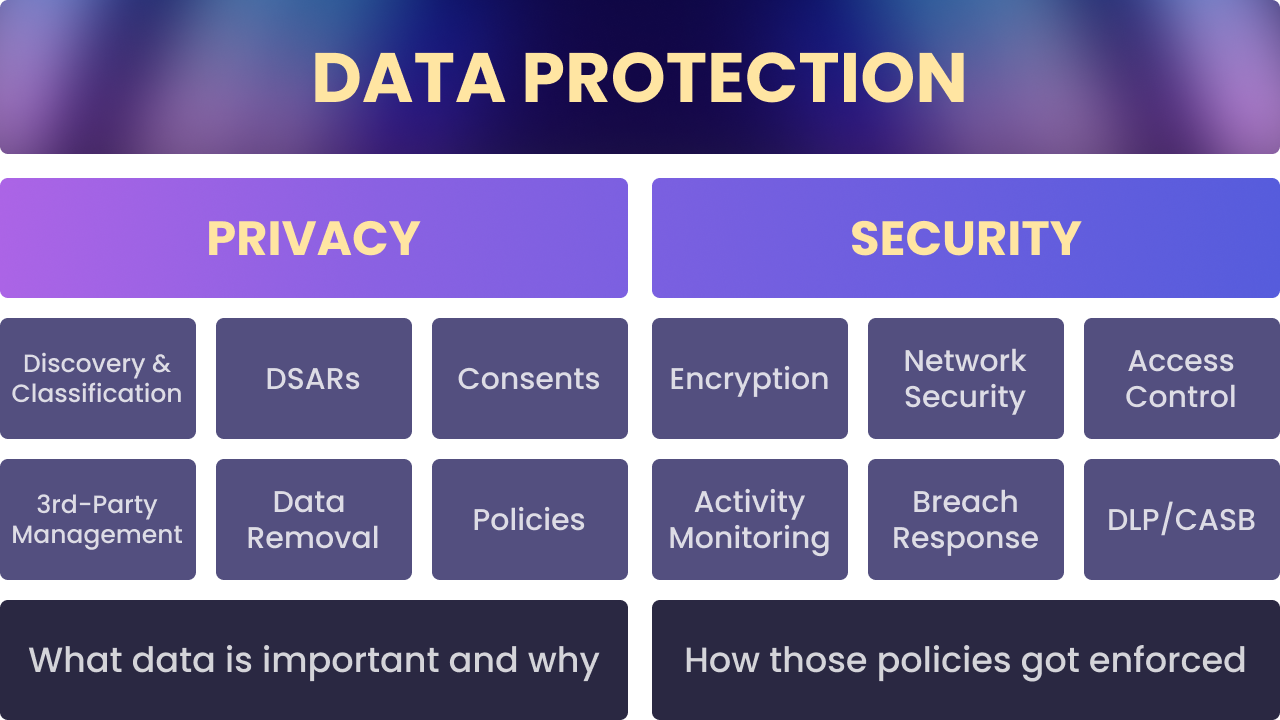
- Data privacy is about managing how data is collected, shared and used.
- Data security, on the other hand, protects data from external attackers and malicious insiders.
Why Is Personal Data Privacy So Important?
This is because data privacy is not only about the security and rights of individuals, but also about fairness and trust in society as a whole:
- Personal security. Attackers may use personal information to conduct unauthorized financial transactions or illegal activities. Therefore, protecting personal data can prevent identity theft, fraud and other forms of cybercrime.
- Privacy. Everyone has the right to control their personal information and decide when, how and to what extent it is shared with others. This is a fundamental right to privacy.
- Trust. Businesses and organizations that protect user privacy are able to build and maintain user trust. Loss of data privacy can lead to customer loss and damage to brand reputation.
- Legal Requirements. Many countries and regions have strict data protection laws that require companies to protect the privacy of personal data.
- Data Misuse. Without effective privacy protection, personal data can be misused for unethical business practices, discriminatory decision-making or political manipulation.
- Preventing discrimination. Protecting personal data privacy prevents discriminatory behavior in areas such as employment, insurance, and financial services, and ensures that everyone is treated fairly.
Want to prevent your business data from being stolen?
Start using Nstbrowser for Free!
Do you have any wonderful ideas and doubts about web scraping and Browserless?
Let's see what other developers are sharing on Discord and Telegram!
Privacy is a fundamental human right in a free society, just like the right to freedom of expression. Personal data can be misused in many ways if they cannot be kept confidential or if people do not have the ability to control how their information is used:
- Criminals can use personal data to deceive or harass users.
- Information owners may sell personal data to advertisers or other third parties without the user's consent, which may result in the user receiving unwanted marketing or advertising.
- When a person's activities are tracked and monitored, this can limit their ability to express themselves freely, especially under repressive governments.
6 Laws to Govern Data Privacy
These laws share the goal of protecting personal data privacy, preventing data misuse, and ensuring transparency and fairness in data processing.
While each law has its own unique provisions and requirements, they all emphasize the importance of protecting personal data.
- General Data Protection Regulation (GDPR)
- California Consumer Privacy Act (CCPA)
- Personal Information Protection Law (PIPL)
- Privacy Act
- Data Protection Act (DPA)
- Lei Geral de Proteção de Dados Pessoais (LGPD)
3 Fundamental Objectives of Data Security
The 3 fundamental objectives of data security are Confidentiality, Integrity and Availability, often collectively referred to as the CIA or CIA Triangle.
- Confidentiality: Information must be available only to authorized parties.
- Integrity: Information must be consistent, trustworthy and accurate.
- Availability: Information must remain accessible to authorized parties even in the event of a failure (little or no disruption).
What Are Fair Information Practices?
Fair Information Practices are a set of guidelines for data collection and use. These guidelines were originally proposed in 1973 by an advisory committee to the U.S. Department of Health, Education and Welfare.
They were later adopted by the International Organization for Economic Co-operation and Development (OECD) in its Guidelines for the Protection of Privacy and Transborder Flows of Personal Data.
Fair information practices include:
- Transparency
- Data collectors should make clear to individuals how their data will be collected, used, stored and shared.
- Consent
- Before collecting personal data, explicit consent of individuals must be provided.
- Users should have the right to withdraw consent and organizations should respect and enforce that decision.
- Use Limitation
- Personal data should only be used for the purpose stated when it was collected and should not be used for other purposes without the individual's consent.
- Data Quality
- Personal data collected should be accurate, complete and, where necessary, up-to-date.
- Data should be retained only for the time necessary to achieve the specific purpose.
- Security Safeguards
- Organizations should take reasonable technical and organizational measures to protect personal data from unauthorized access, disclosure, modification or destruction.
- Individual Participation
- Users have the right to access their personal data and have the right to request that inaccurate data be corrected, updated or deleted.
- Individuals should be able to challenge data processing and receive a reasonable
explanation.
- Accountability
- Data controllers and processors should be accountable for their data protection practices and be able to demonstrate compliance.
- Organizations should regularly review and improve their data protection measures.
- Data Minimization
- Only the minimum amount of data required to achieve a specific purpose should be collected.
- Avoid collecting and processing unnecessary personal information.
- Purpose Specification
- When collecting data, it should be clearly stated for what purpose the data will be used.
- The purpose should be determined before or at the time of collection and limited to legitimate and proper purposes.
- Accountability and Auditing
- Organizations should establish appropriate mechanisms to regularly review and audit their data protection practices.
- Ensure that data processing is consistent with the stated purpose and applicable laws and regulations.
How Can Users Effectively Protect Their Data Privacy?
1. Use strong passwords and double authentication
- Create strong passwords that include a combination of letters, numbers and special characters.
- Use different passwords for different accounts to avoid password reuse.
- Enable double authentication (2FA) to add an extra layer of security.
2. Handle personal information with care
- Do not share personal information freely on social media or untrusted websites.
- Use pseudonyms or anonymized identities to protect your privacy.
3. Use encrypted communications
- Use end-to-end encrypted communication tools such as Signal, WhatsApp and Telegram.
- Ensure that email and file transfers use encrypted protocols such as SSL/TLS.
4. Install and use security tools
- Install reliable anti-virus and anti-malware programs and scan your system regularly.
- Use a virtual private network (VPN) to hide IP addresses and encrypt Internet traffic to protect privacy.
5. Use Nstbrowser
Nstbrowser adopts IP rotation and real browser fingerprint to hide your specific IP address and fingerprint information, effectively avoiding the leakage of personal data. All aspects of data privacy protection.
How Can Enterprises Effectively Protect Data Privacy?
1. Implement a data protection policy
Develop and implement a comprehensive data protection policy to ensure employees understand and comply with privacy protection regulations and best practices.
2. Data encryption
Encrypt sensitive data in storage and transmission to ensure that even if data is intercepted, it cannot be read by unauthorized personnel.
3. Access control
- Role-based access control (RBAC) is used to restrict employee access to data related to their job responsibilities.
- Regularly review and adjust access rights to ensure that only those who need to access the data can do so.
4. Third-party risk management
- Enter into data protection agreements with third-party vendors and partners to ensure they adhere to privacy protection standards.
- Regularly assess third party security measures and compliance to ensure data security.
5. Use Nstbrowser
Nstbrowser adopts specialized technology to protect the enterprise-grade data and privacy. Maintain the business and work security of the organization.
- Cloud browser for secure access, isolated from real local information.
- One-time access setting avoids information leakage.
- Real-time monitoring of illegal intrusion and malicious crawling activities to protect data security.
More






